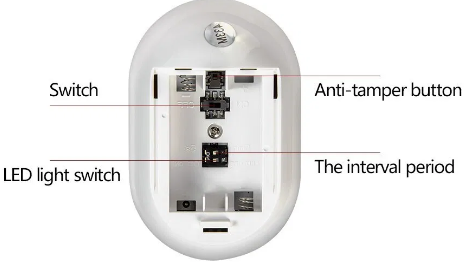
Anti-tampering
These check the system’s ability to detect and respond to tampering, which can take several forms. An intruder may use a brute force attack, like the radio signals emitted by sensors with electromagnetic frequencies. Other prosaic techniques include interrupting the power supply or disconnecting the Wi-Fi – effective if there’s no cellular back-up. To defeat these tampering techniques, sophisticated technology needs to be integrated into the system. Only then can it pass these tests.